Your auditor just asked who accessed production secrets last Tuesday. Do you have the answer?
AES-256 encryption, row-level access control, and complete audit trails for every secret access. Deploy in minutes instead of weeks. No infrastructure to maintain.
Security controls that pass the audit
Every feature your security team needs. No infrastructure to deploy or maintain.
AES-256-GCM Encryption
Every secret is encrypted at rest using AES-256-GCM via Supabase Vault. Zero-knowledge architecture — your secrets are never stored or transmitted in plain text.
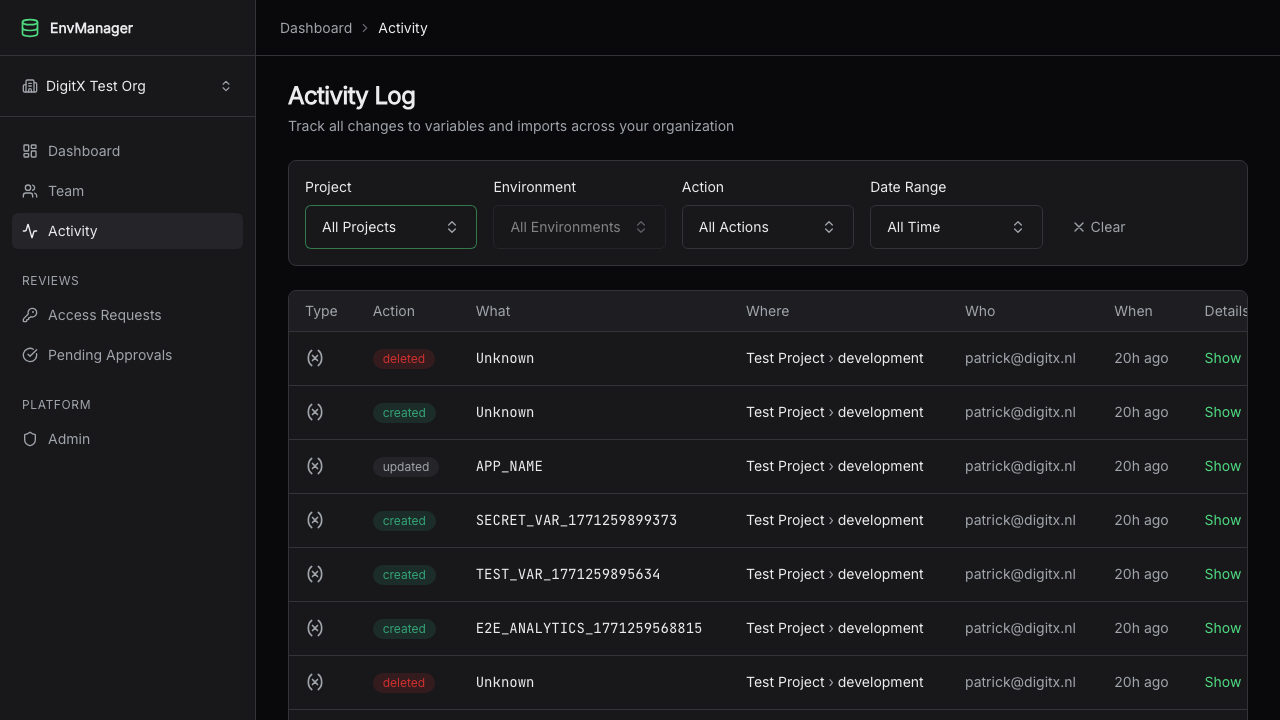
Audit Logs That Satisfy Auditors
Every access, modification, and export is logged with timestamp, user ID, and action type. Export full audit reports per project for compliance reviews.
Granular Role-Based Access
Admin, Editor, and Viewer roles with per-environment permissions. Control exactly who can read, write, and approve changes to production secrets.
Production Approval Workflows
Require single or two-person approval before production changes go live. Automatic expiration for pending approvals. Full audit trail on every decision.
Time-Limited Secret Access
Team members request access to view secret values. Admins grant temporary, time-limited access. Every request and grant is logged.
Org-Wide Naming Enforcement
Define and enforce naming conventions for every variable. Audit existing variables in bulk. Validate automatically on every create, import, and update.
Full Version History & Disaster Recovery
Every change is versioned with full rollback capability. Take environment snapshots before deployments. Restore to any point in time.
Schema Validation
Define schemas with type, format, and required rules. Validate in the UI, CLI, and CI pipeline. Prevent misconfigurations before they reach production.
Self-Hosted & Cloud Integrations
Deploy to Vercel, Railway, Render, GitHub Actions, Dokploy, and Coolify. Custom CA certificate support for on-premise infrastructure.
Compliance-ready from day one
Comprehensive logging, granular access controls, and encryption standards that satisfy auditors. No months-long implementation project.
Audit-Ready Access Logs
Every secret access and modification is logged with timestamps, user identifiers, and action types. Exportable per-project for auditor review.
Documented Access Control Model
Clear role definitions (Admin, Editor, Viewer) with per-environment permission matrices. Ready for security assessments and vendor questionnaires.
Industry-Standard Encryption
AES-256-GCM encryption at rest via Supabase Vault (pgsodium). Secrets are never stored or transmitted in plain text.
Change Approval Controls
Production changes require explicit approval. Two-person sign-off mode available. Automatic expiration prevents stale approvals.
Framework alignment
SOC 2
Encryption at rest, audit logging, and access controls aligned with SOC 2 Trust Services Criteria.
GDPR
Data protection controls, access logging, and role-based permissions for EU data handling requirements.
HIPAA
Encrypted storage, access audit trails, and role-based controls suitable for protected health information.
ISO 27001
Information security management controls including encryption, access control, and change management processes.
Enterprise security without the enterprise implementation timeline
Deploy in minutes, not months. 14-day free trial with no credit card required.