Stop sharing secrets over Slack
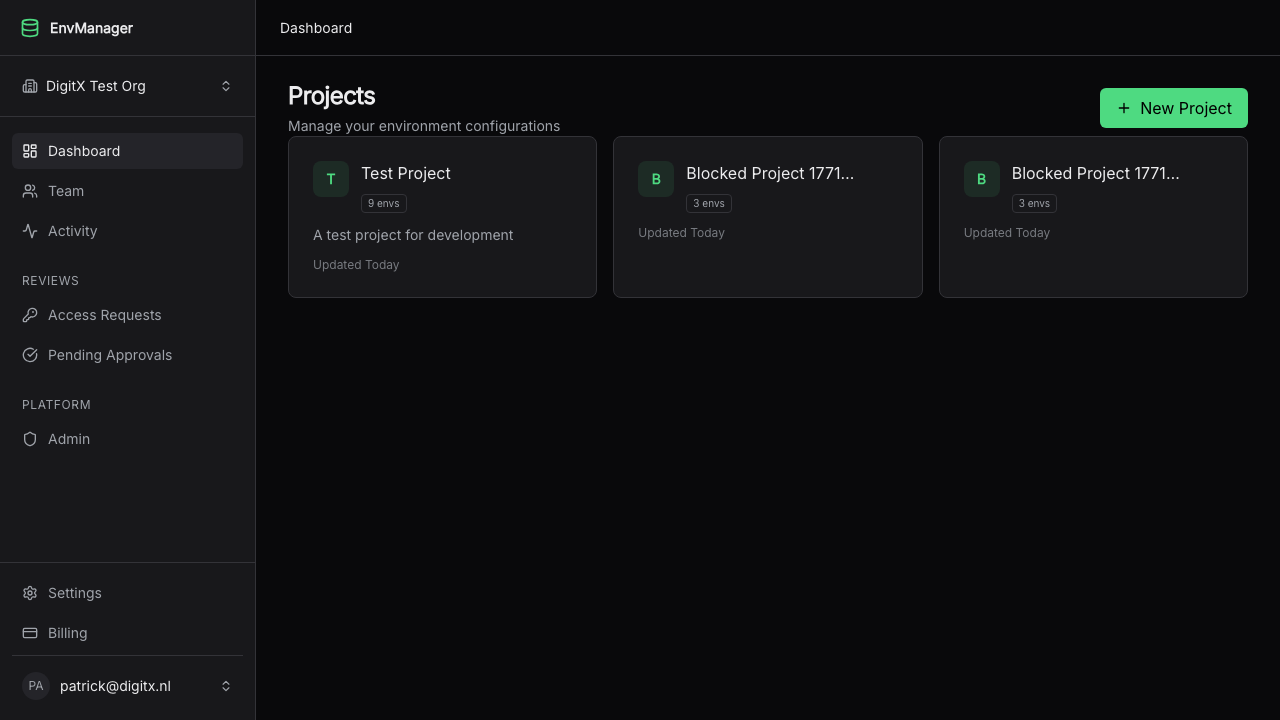
EnvManager replaces .env files passed through chat, email, and sticky notes with encrypted, versioned, role-based secret management. Set up in 2 minutes.
Trusted by teams shipping to production
From scattered .env files to secure vault in 3 steps
Import your .env files
Paste or drag-and-drop your existing .env files. EnvManager encrypts every value with AES-256 on import.
Set roles and environments
Define who can access production vs staging. Invite your team with granular, per-environment permissions.
Sync with one command
Run envmanager pull to sync secrets to your local machine or CI/CD pipeline. Done.
Security that doesn't slow you down
Every .env shared over Slack is a secret exposed. Every developer who leaves still has your production keys. EnvManager fixes both.
Know exactly who changed what, and when
Every secret change is versioned with an immutable audit trail. Roll back a bad rotation instantly. Pass compliance audits without scrambling.
Your secrets never leave the vault unencrypted
AES-256 encryption at rest via Supabase Vault. Secrets are decrypted only at the moment of access, by authorized users only.
Interns can't access production
Grant access per project and environment. Developers see staging, leads see production. Revoke instantly when someone leaves the team.
One command. All your secrets. Locally.
No more asking teammates for the latest .env. Pull secrets straight from the vault to your machine or CI/CD pipeline with one CLI command.
$ envmanager pull
Synced 24 secrets to .env
$ npm run dev
Call Stripe from your static site without leaking keys
Static sites expose every API key in the browser. Proxy functions route those calls through EnvManager, injecting secrets server-side. No serverless function to write, no infrastructure to manage.
// No API key in your frontend code
const res = await fetch(proxyUrl, {'{'}
method: 'POST',
headers: {'{'} 'x-proxy-token': token {'}'},
body: JSON.stringify({'{'} to: email {'}'}),
{'}'})
// EnvManager injects BREVO_API_KEY server-side
// Your secret never reaches the browser
Connects to your existing stack
Sync secrets directly to Vercel, Railway, Render, GitHub, Google Cloud, Azure, and more. No copy-pasting between dashboards.
The cost of doing nothing
Most secret leaks aren't from sophisticated attacks. They're from your team's daily workflow.
.env files in Slack
Searchable by anyone in the workspace forever. One leaked API key costs an average of $1.2M to remediate.
No offboarding
When a developer leaves, do you rotate every secret they had access to? With .env files, you can't even know which ones they saw.
Secrets in git history
Accidentally committed a key? Even after removing it, it lives in git history forever. Bots scan public repos in seconds.
Your .env files are a liability. Fix it in 2 minutes.
Free for small teams. No credit card required. Import your existing .env files and start syncing secrets securely.